Have you ever tried to find someone, an ex-employee, a key witness, or someone who has gone dark, only to hit a wall, even after hiring a private investigator?
Why do most “locate reports” come up short when the person you’re trying to find actually doesn’t want to be found? And why is it so hard to get real answers when you need them most?
Last week, I shared some interesting case studies to find people, but in this article, I’ll share why most people-search services and investigative firms fail, even when they have access to professional databases. I’ll also show you the tools, methods, and decision-making frameworks we’ve used to locate individuals others could not, even after multiple firms had tried and failed to find these hard-to-find people.
You’ll learn:
- Why most locate reports are just data dumps (and what that really means for your case)
- The tools we rely on when someone’s gone dark
- Real-world tactics that go far beyond software or subscriptions
Because in the world of serious investigations, it’s not about magic tools—it’s about experience, strategy, and knowing where to look when the usual methods fall flat.
When Typical Locate Reports Fail
If you’re trying to track down someone like Jane—a stay-at-home mom who’s lived at the same address with her husband and kids for the last 15 years—then a standard locate report might actually work. Running her name through professional databases like IDI or TLO, or even a commercial subscription service like Intelius, TruthFinder, or Spokeo, could turn up the right address. These tools tend to do well when the person hasn’t moved much, has kept consistent records, and hasn’t tried to hide.
And then there are the cases where we’re given almost nothing to start with. A first name, maybe a city, a former employer, or sometimes just a vague connection. Like “He used to work construction in Phoenix,” or “She might’ve gone to school in North Carolina.” No last name, no date of birth, no address history. That’s when the real work begins. These aren’t just data searches; they’re puzzles. In those situations, it’s about pattern recognition, creative pivots, and looking where others never think to look. You can’t just run a report; you must build the story from scraps.
We get called in when the usual tools fall flat. When someone has changed names, moved without leaving a forwarding address, or deliberately scrubbed their digital footprint. That’s when the copy-and-paste locate reports from cheaper services not only fall short, they give a false sense of confidence. They tell you what might be true, not what’s provable. And in legal or high-stakes situations, “maybe” doesn’t cut it.
Common Mistakes Investigators Make, and How to Avoid Them
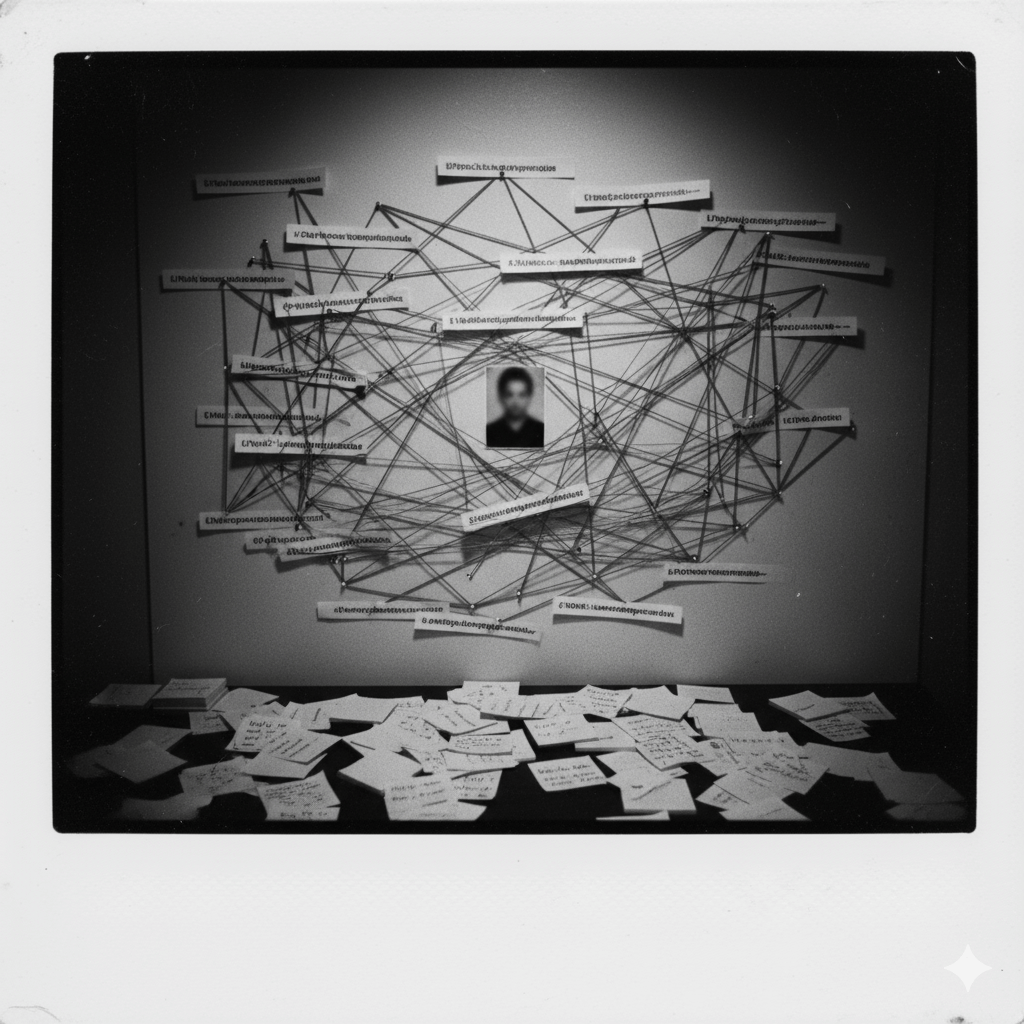
In the majority of failed investigations we’re called in to clean up, one thing stands out: the previous investigator relied on a single source of information and came up empty.
Law firms often send us the locate report from their last PI, and what we see is almost always the same: a cut-and-paste export from a professional database like TLO, IDI, or Delvepoint. That’s it. No verification, no context, no narrative. Just raw data that assumes the last known address is current and that every record is accurate.
Here’s the hard truth: dumping data into a PDF isn’t an investigation; it’s wishful thinking dressed up as a deliverable.
If you want real results, you have to think beyond the screen.
Common Mistakes That Cause Investigations to Fail
Below are some of the most common mistakes we see other investigators make, and why they fail:
Overreliance on a Single Database
Too many investigators pull data from one source, like TLO, and assume the most recent address or phone number listed is valid. But no single database has everything. Each pulls from different public records, credit headers, utility info, and scraping sources, all of which have gaps.
Why it fails: If the person has changed names, moved recently, or taken steps to avoid detection, that single-source data may already be outdated, or intentionally misleading.
No Cross-Verification of Key Data Points
Even if you find an address in a database, that doesn’t mean the person lives there. Good investigators cross-verify that information with other records: DMV data, voter rolls, property deeds, court filings, and more.
Why it fails: Without a second or third source confirming the same address, you’re building your case on a maybe, and in legal or high-stakes matters, “maybe” isn’t good enough.
Lack of Context or Narrative
Dumping data ≠ solving the problem. Raw data can’t tell a story. It doesn’t explain why someone moved, or how different addresses might connect through a relative, job, or phone record. Or if the address is just one of many database errors.
Why it fails: Dumping a dozen addresses into a report without explaining their timeline or relevance leaves clients confused and misled. Worse, it can send legal teams in the wrong direction.
Failing to Pivot When the Trail Goes Cold
When the database comes up short, some investigators stop. They assume that’s the end of the road, or the client is unwilling to pay for it. But real investigations are about creative pivots like using vehicle sightings, licensing records, breach data, or social media breadcrumbs to find a new lead.
Why it fails: People who don’t want to be found leave misleading trails on purpose. You can’t out-database someone who’s hiding. You need real-world logic and lateral thinking.
Assuming the Client Won’t Notice
Some firms cut corners, assuming the client won’t know the difference between a thorough search and a recycled report. This might be a news flash to some people, but law firms have access to TLO, just like investigative firms. That might work once, but not twice. Law firms, in particular, can spot a lazy locate when they see one, and if they’re sending that report to us, it means they already know it didn’t deliver.
Why it fails: Credibility matters. And once your client sees that all you did was regurgitate a database export, they won’t call again.
What Actually Works
There’s no magic tool or one-size-fits-all method. Real results come from layering multiple data sources, confirming what’s real, and using logic, pattern recognition, and persistence to build a narrative that makes sense.
It’s not about copying data. It’s about connecting dots.
How Real Investigations Begin: What You Need Before You Start
When I say I’ve been able to “find people,” I usually mean one of two things: I’ve got them on the phone, or I have an address, verified through multiple sources, in hand. While email addresses can be useful, in most of my work, they’re too easy to ignore to rely on.
To actually locate someone, you need more than just a name. One piece of information rarely does the job. But give me two or three reasonably solid identifiers, like where they lived, worked, or went to school, and things start to click. With three good data points, I can usually track someone down. With only one, it’s often a guessing game, unless the person has a unique name.
Too often, I see other investigators run a name through one or two databases like IDI, TLO, Delvepoint, or Tracers, grab the most recent address, and move on. That kind of surface-level work doesn’t cut it.
I believe in confirming everything. If I get an address, I want a second or third source to back it up. That might be voter rolls, DMV records, property deeds, or anything else official that strengthens the case. When you’re serious about results, you don’t settle for maybe, you prove it.
Is It Always Possible to Find Someone? Not Exactly.
I like to say everyone can be found with enough time, money, and persistence. But those things aren’t unlimited. Not every case allows for hours of stakeouts or deep dives into digital trails. The real skill lies in knowing the available tools and choosing the smartest, most efficient path forward.
That said, the idea that everyone is findable just isn’t true. Sometimes the details are too vague. Sometimes the request itself feels off. I’ve had more than a few people ask me to find someone they sat next to on a flight last Tuesday, or someone they “forgot” to get a number from after a two-minute conversation.
One person once asked me to find “a guy named Tony” whom they’d met at a music festival in 2017. No last name, no city, not even a photo—just a memory of him wearing a red flannel shirt and liking old cars. That’s not an investigation. That’s a long shot at best, and throws up some red flags at worst.
What It Really Takes to Track Someone Down
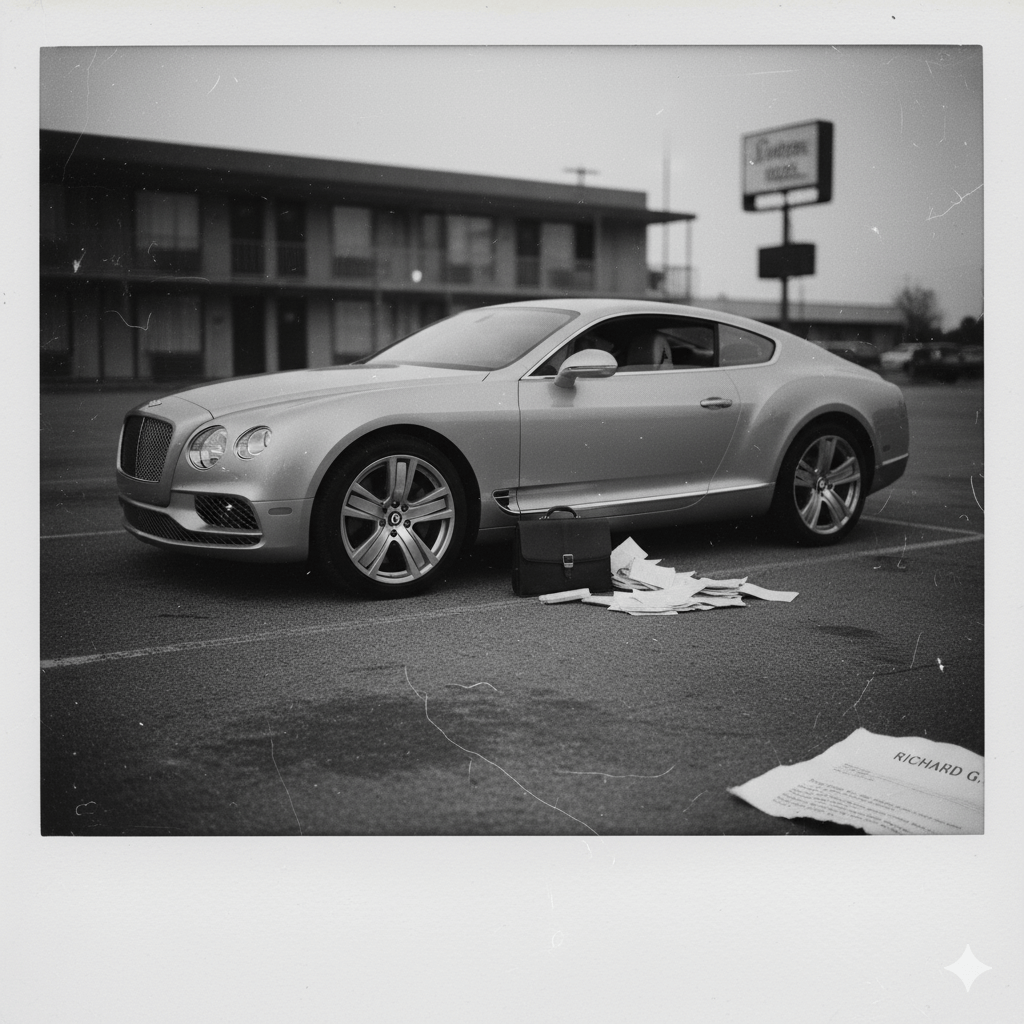
Most of my work focuses on U.S.-based cases, primarily involving white collar matters. I’m not chasing international scammers or fugitives from the Most Wanted list. My cases are more grounded, but no less complex.
Often, I’m hired to locate someone who needs to be served in a legal matter. It could be someone covering their tracks or simply hard to pin down due to limited details, a common name, or a transient lifestyle.
In other cases, it’s about finding potential witnesses in civil or criminal matters, like Mike, an Uber driver in Chicago, identified only by a blurry profile picture. Sometimes it involves tracking down former employees who may have crucial knowledge, like Jeffrey Jones from Walmart in Bentonville.
And every so often, the challenge is locating someone with a common name and almost no supporting details, the kind of search where experience, persistence, and a bit of intuition make all the difference.
The Best Tools Private Investigators Use to Find Someone
People always want the list. “What tools do you use?” Here’s the truth: it’s less about having access and more about knowing how to use what you’ve got.
Some of the tools below are not so secret, but they might not be used often to track down people. We’ve worked hundreds of complex people-finding cases, including those that other firms gave up on.
Here are some field-tested tools and techniques we regularly use:
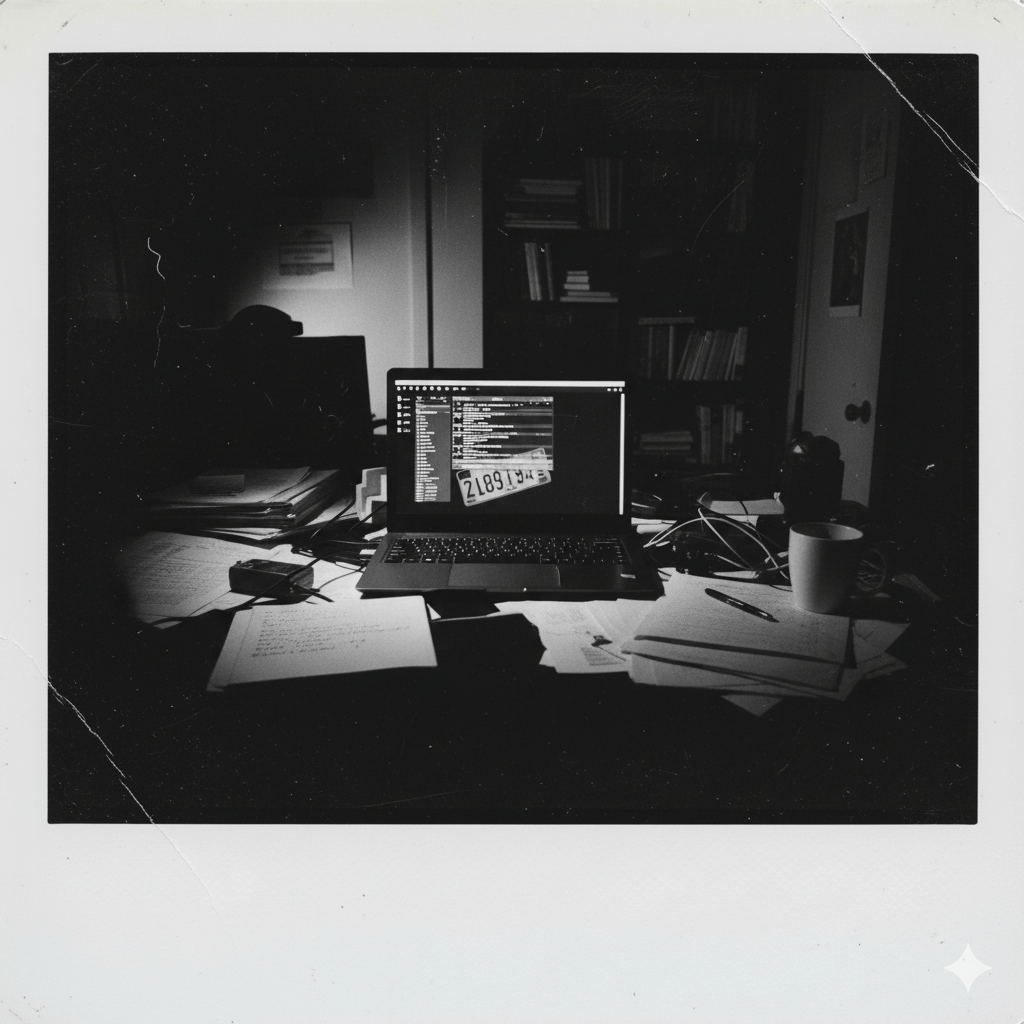
Professional People-Finding Databases (IDI, Delvepoint, etc.)
Never rely on just one. Each source has gaps. Professional investigative databases such as IDI, TLO, Delvepoint, Tracers, and IRB Search will help get a fuller picture. (I’ve had mixed success with commercially available “investigative” database websites like TruthFinder, Spokeo, BeenVerified, and Intelius, so with those, I would proceed cautiously.) One might give you a phone number, another a linked address. You wouldn’t believe how many “unfindable” people pop up once you combine enough datasets together.
License Plate Reader and Vehicle Sightings Databases
LPR databases, like those from DRN or accessible for investigators through TLO, Delvepoint or IRB Search, can be game-changers. They track where a vehicle has been spotted on city streets, in parking lots, or in driveways, using a network of vehicle-capturing cameras that roam the streets. In tough cases, when nothing else is working, a single plate hit can confirm where someone actually is. People may ditch their phone or move without a trace, but most don’t give up their car. Following the vehicle often leads to the person.
Social Media OSINT Tools and Username Tracking
Some of the most powerful clues hide behind usernames, email addresses, and phone numbers. Tools like OSINT.Industries help link social media accounts to usernames, email addresses, and telephone numbers, and Skopenow can identify accounts. WhatsMyName is useful for finding usernames across platforms, and ShadowDragon is great for linking social media accounts and conducting sophisticated, deep analysis and tracing.
Litigation Research Tools (County Courts, Pacer, Judy Records, LexisNexis, etc.)
Local county courts are a great place to start. Even the most minute detail in a traffic infraction might reveal something crucial. For deeper research, check Pacer, Recap, or Judy Records. For more comprehensive litigation coverage, you can use paid databases like LexisNexis, BloombergLaw, or Westlaw.
DMV Records and Driver Data
With permissible purposes (see the DPPA), DMV driving records and vehicle data are powerful tools for locating people. Investigative databases such as IDI, TLO, Delvepoint, Tracers, and IRB Search have some data, but it’s better to go directly to the source. Logan Registration and Denspri are excellent options for accessing individuals’ state records.
Breach Data and Credential Leaks (e.g., Dehashed, Darkside)
In a world where apps get hacked constantly, old email addresses become breadcrumbs. We’ve cracked cases using login data from parking apps, pet sites, and other random corners of the web most people forget ever existed. There are reasonably priced commercially available tools like Dehashed and Snusbase, or more sophisticated tools like Darkside from District 4 Labs.
Facial Recognition Software (e.g., FaceCheck.ID and PimEyes)
Usage of facial recognition tools may be subject to legal regulations and ethical considerations, but a few to check out include FaceCheck.ID and PimEyes.
FOIL Requests
Freedom of Information Law (FOIL) requests can be a powerful way to access records that aren’t readily available online. They’re especially helpful for military service or regulatory complaints. The catch? They often take time, and in many cases, time is the one thing we don’t have.
Professional Licensing Records
Many professions require a state-issued license—everything from doctors and nurses to electricians and nail technicians. These records often include valuable details like middle names, education history, employment status, and sometimes even home addresses. When used correctly, licensing data can be the missing link in a search.
Property Records and Deed Searches
Property records, when combined with voting data or DMV hits, can identify exactly where someone is, even if they’re trying not to be found. The local county recorder’s office is a good starting point; more in-depth research can be done on platforms like LexisNexis or Westlaw, which have a vast collection of nationwide property records, where you might find that vacation property in a neighboring state.
Google Dorking and Advanced Search Tactics
Google remains a vital tool for connecting ideas, but most people only understand it in its simplest form. Knowing how to do proper Google dorking can be a key skill. I also like to use the site MillionShort, which effectively filters out sites with too much SEO that always rank at the top, by, for example, allowing you to disregard the top 100,000 most popular sites. It’s like digging for gold in the depths of the Internet.
Employment Information
This can be a tricky area to nail down. The major investigative databases, such as IDI, TLO, Delvepoint, Tracers, and IRB Search, often fall short when it comes to current employment data. But that doesn’t mean you’re out of options. Tools like ZoomInfo and other subscription-based platforms can offer employment history, titles, and contact details. Resume databases such as Monster and Indeed sometimes surface gold, especially if someone forgot an old resume that they posted years ago. And don’t overlook LinkedIn. A Sales Navigator subscription can be incredibly helpful for tracing work history and finding professional connections. Piecing this info together from multiple sources is often the key to confirming where someone works or worked recently.
Real-World Logic: Habits, Patterns, and Gut Instinct
Sometimes it’s not about the tools; it’s about the thing between your ears. Patterns matter. Habits don’t lie. Maintenance workers live close to their job sites. Ex-partners still pick up mail. Homeless individuals still check the same drop spots. Experience teaches you what to try when the software falls short.
What Situations Require More Than Google or a Database Subscription?
Let me be blunt for a second. If you’re relying on Spokeo, Intelius, or a cheap “people search” site to find someone who doesn’t want to be found, you’re wasting your time. These platforms pull from the same shallow public records and are often filled with outdated or incomplete data.
Google isn’t much better when the person you’re looking for has gone quiet, changed addresses, or actively taken steps to disappear. When you’re dealing with serious matters, a $29/month subscription isn’t going to cut it.
Even with a single-source professional database, you may also be wasting your time.
These cases demand layered investigation, access to professional-only databases, and field-tested strategies that uncover what software alone can’t. Real results don’t come from search bars, they come from experience, creativity, and knowing how to go far beyond the screen.
Why We’re Not the Right Fit for Every Case
More often than not, we succeed, not because we have access to some secret master list, but because we know how to think differently. We don’t rely on one tool or one database. We treat each case like a puzzle, and we know where to look for the missing pieces.
But we’re not the right fit for everyone. If you’re just curious about an old classmate, missed your chance to get someone’s number, or are looking for Jane—the stay-at-home mom who’s lived in the same house for 15 years—Google or a basic subscription site might be enough. In cases like that, you don’t need us.
We come in when the search actually matters: when it’s tied to a legal case, a financial stake, or a personal loss, and you’ve already tried the usual routes. That’s when our approach makes a difference.
A client once came to us after months of trying to serve court papers to a man who had vanished. They’d tried three different firms. Nothing worked. We found him in four days, because we didn’t stop at databases. We followed the trail until it made sense.
If your situation feels like that, and you’re ready for someone to actually solve the puzzle, we’re here. Just know that we can’t promise magic.
Final Thoughts: Finding People Takes More Than a Database
In the past, you may have tried to locate someone using online search tools or hired a firm that delivered little more than a database printout, only to end up with more questions than answers. And if the stakes were high, that kind of uncertainty probably wasn’t just frustrating but costly as well.
Now you’ve seen the difference that layered tools, strategy, and real investigative experience can make. Whether it’s identifying the right John Smith in a city of hundreds or tracking down someone who’s gone completely off the grid, the right process makes all the difference. Moving forward, if you’re facing a legal, personal, or financial matter where getting it right actually matters, and you’re tired of surface-level work, we’re here to help. We don’t deal in guesses. We deal in results.